If you’ve ever tried to connect your app to a secured web API hosted on an identity server, you know it can feel like trying to open a high-tech vault without a key. You’re not alone if you’re finding it tricky.
But what if you had a straightforward guide to make it easy and stress-free? This article is here to do just that. Imagine effortlessly accessing the data you need, with every step laid out clearly and simply. You’ll gain a deeper understanding of how these systems work, and you’ll feel more confident tackling tech challenges.
Ready to unlock the secrets? Dive in and discover how you can master this process with ease.
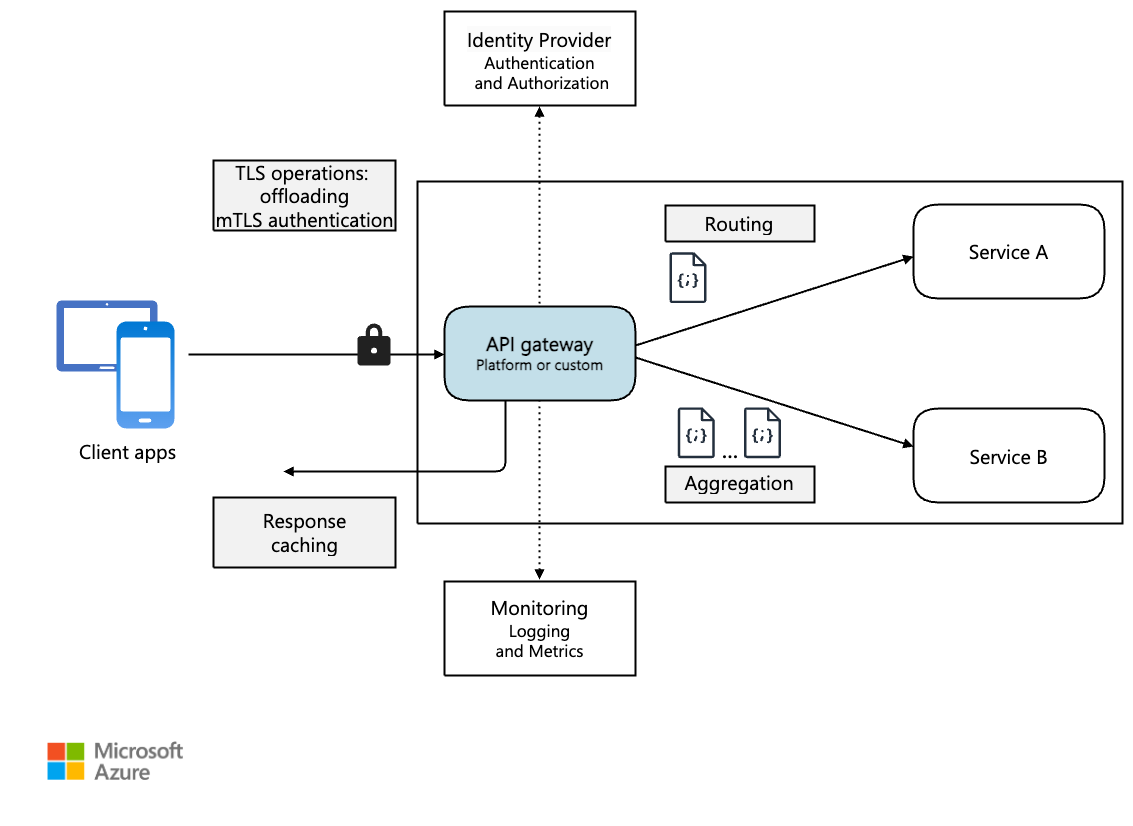
Credit: learn.microsoft.com
Understanding Identity Server
Identity Server helps keep APIs safe. It checks who wants to use the API. Only trusted users can enter. This makes sure data stays safe. Security is the main job. It watches for bad people. Protects from attacks. Keeps info private.
Identity Server has parts that work together. Clients ask for access to the API. Resources are what the API protects. Identity tells who a user is. Tokens are like keys. They open the door to the API. Each part has a special job. Together, they make the API safe.
Setting Up Identity Server
First, download the Identity Server package from the official website. Next, unzip the package. Open the folder and find the setup file. Double-click the setup file to start the installation. Follow the on-screen instructions carefully. Choose the default settings for ease. Make sure your computer meets the system requirements. Once installed, you will see a new icon on your desktop. Click it to launch the Identity Server.
Open the Identity Server dashboard. Click on the configuration tab. Enter your server details like name and address. Set up a secure password. Make sure to use letters, numbers, and symbols. Save your settings. Test the connection to ensure everything works. You can now start using the Identity Server to secure your API.
Securing Web Apis
OAuth2 is a popular protocol to secure web APIs. It allows apps to access user data without sharing passwords. Users can trust apps because their passwords stay safe. OAuth2 works by issuing tokens. These tokens let apps access data for a short time. They expire quickly to keep data safe.
Tokens are like keys. They open doors to data. Each token is unique. It identifies the user and what they can access. Tokens are easy to use. They work with many devices. Devices include phones, tablets, and computers. Tokens protect user data. They ensure only the right people see it.
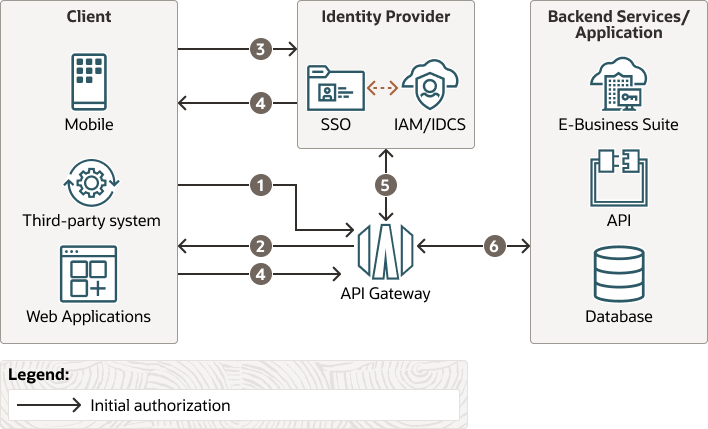
Credit: docs.oracle.com
Client Registration
First, create your client app. This app will connect to the server. Choose a name for your app. Make sure the name is unique. You will need an App ID. This ID helps the server recognize your app. Don’t forget to write it down.
Register your app on the server. This step is important. The server needs to know your app. You will enter the App ID during registration. After this, your app can talk to the server.
Permissions are like rules. They tell what your app can do. Decide what your app needs to do. List these actions clearly. You might need to read data. Or you might need to write data. Define these actions carefully.
Make sure to set permissions right. Too many permissions can be bad. Only give permissions that are needed. This keeps your app secure. Double-check the permissions before saving. This is an important step.
Accessing Secured Apis
APIs need access tokens for security. First, you must ask for a token. This is done by sending a request. The server checks if you are allowed. If yes, it gives you a token. This token is a key. Use it to unlock the API. Without this token, you cannot enter.
Tokens have a time limit. They expire after some time. Always check the token’s time. Before it expires, get a new token. The process is the same. Send a request to the server. The server gives you a fresh token. This keeps your access safe and active.
Integrating With Applications
Securing web APIs with Identity Server ensures safe data exchange. Learn to access these APIs efficiently. Follow clear steps to integrate applications smoothly.
Connecting Client Apps
Client apps talk to the web API. They need to be securely connected. This is important for data safety. Identity Server helps with security. It checks if the app can access the API. Apps must have correct tokens. Tokens are like keys. They open doors to data. Keep tokens secret and safe.
Api Call Examples
Here are some examples of calling the API:
- GET Request: Used to fetch data. Easy and common.
- POST Request: Sends new data. Careful with what you send.
- PUT Request: Updates existing data. Needs correct information.
- DELETE Request: Removes data. Use wisely.
These calls need authentication. Always check if you have access. Follow the rules for safe access.
Troubleshooting Common Issues
Navigating secured web APIs can be tricky. Ensure your client is configured to handle authentication tokens properly. Double-check API permissions and endpoint URLs for smooth access.
Token Validation Errors
Token errors happen often. Invalid tokens cause issues. Check token expiry dates. Ensure tokens are signed correctly. Use correct signing algorithms. Validate token audience and issuer. Ensure token scopes match API needs. Check for missing claims. Incorrect claims can lead to errors. Double-check token settings in server. Monitor logs for error patterns.
Connection Failures
Connection problems can be frustrating. Ensure network settings are correct. Check server URL and port. Verify server is online. Use proper authentication methods. Confirm firewall settings allow traffic. Check SSL certificates are valid. Expired certificates block connections. Review server logs for connection issues. Test connection from different devices. Network congestion can affect performance.
Best Practices
Use strong authentication methods. Ensure API keys and tokens are stored safely. Regularly update and patch your system. Protect data with encryption. Limit access to sensitive information. Monitor API activity for suspicious behavior. Validate user inputs to prevent attacks. Use firewalls to secure your network. Implement rate limiting to control traffic. Educate your team on security protocols. Regularly audit your security measures. Always be vigilant against threats.
Optimize API calls for speed. Minimize data transfer size. Use caching to reduce load times. Compress data to save bandwidth. Scale servers to handle more requests. Monitor server performance regularly. Use efficient algorithms for processing. Limit unnecessary requests. Ensure fast database queries. Balance load across servers. Reduce server response times. Keep code clean and efficient. Regularly review and improve code. Aim for smooth user experiences.
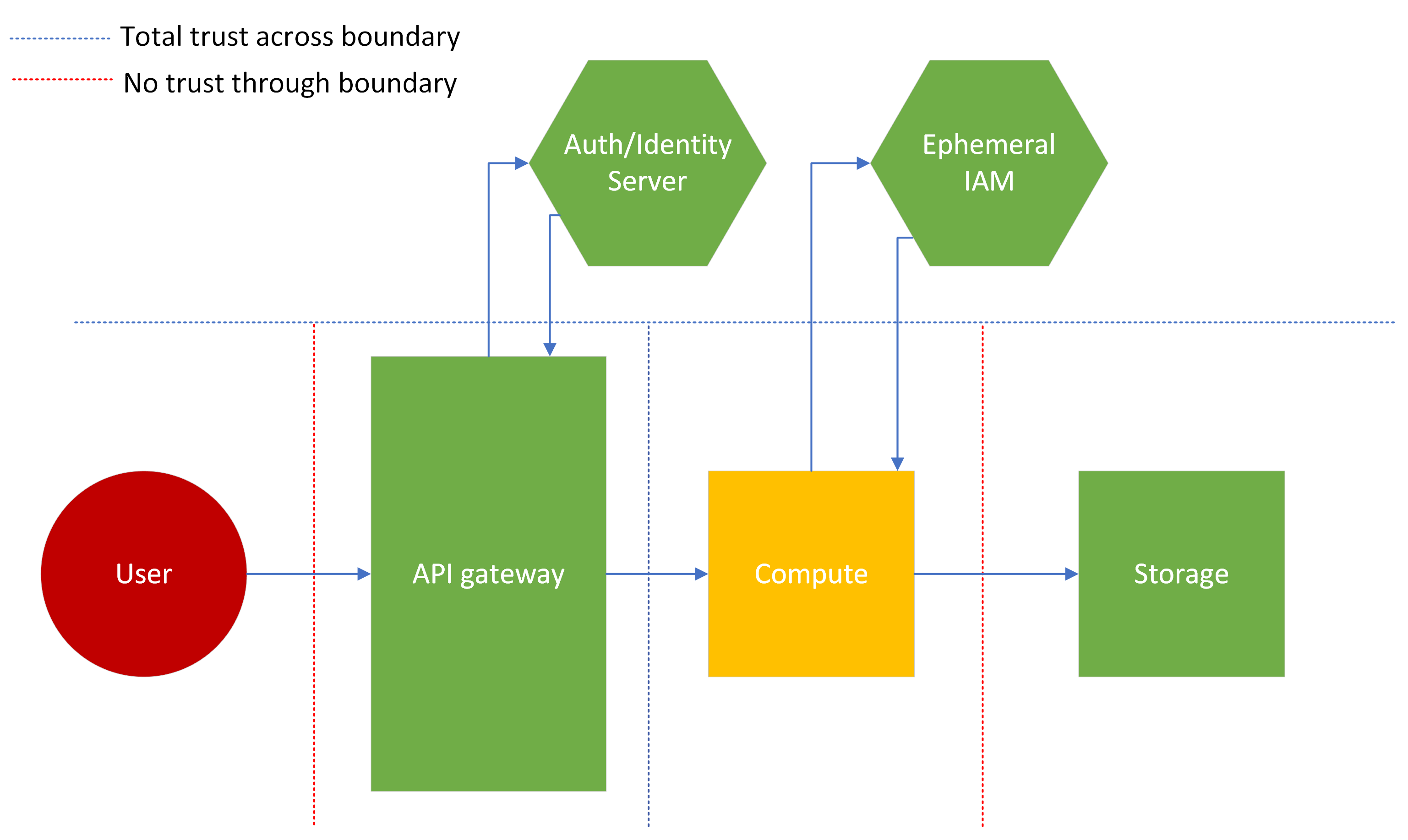
Credit: cheatsheetseries.owasp.org
Frequently Asked Questions
What Is Identity Server Used For?
Identity Server is used for securing web APIs and managing user authentication. It implements OpenID Connect and OAuth 2. 0 protocols to provide single sign-on and secure access. This enables applications to authenticate users and authorize their access to resources efficiently.
How Can I Consume A Secured Web Api?
To consume a secured web API, first obtain an access token from the Identity Server. Use this token in your API requests by including it in the Authorization header. This ensures that your requests are authenticated and authorized.
What Is An Access Token?
An access token is a credential used to access secured resources on a server. Issued by an Identity Server, it contains information about the user and permissions. It is included in API requests to authenticate and authorize the user.
Why Use Oauth 2.0 For Web Apis?
OAuth 2. 0 is used for web APIs to provide secure delegated access. It allows applications to access resources on behalf of users without exposing their credentials. This ensures secure and efficient authentication and authorization processes.
Conclusion
Securing web API access is crucial. Follow the steps outlined above. Understand your Identity Server setup. Implement proper authentication methods. Use tokens for secure communication. Test your connections regularly. Troubleshoot any authentication errors. Ensure your API remains protected. Keep your systems updated.
Stay informed on security practices. Enjoy safe and efficient API interactions. This knowledge boosts your tech skills. Your API security matters.



